 This is the second part of a five part tutorial that will show you how to install a full featured email server on your Raspberry Pi. This tutorial covers Dovecot, which provides SASL authentication and IMAP capabilities.
This is the second part of a five part tutorial that will show you how to install a full featured email server on your Raspberry Pi. This tutorial covers Dovecot, which provides SASL authentication and IMAP capabilities.
The parts are:
The Introduction & Contents Page (read first)
Raspberry Pi Email Server Part 1: Postfix
Raspberry Pi Email Server Part 2: Dovecot
Raspberry Pi Email Server Part 3: Squirrelmail
Raspberry Pi Email Server Part 4: Spam Detection with Spamassassin
Raspberry Pi Email Server Part 5: Spam Sorting with LMTP & Sieve
Fixing the errors that appeared during dovecot installation
In part 1, when you installed Dovecot I mentioned that you might see some errors like this:
Creating config file /etc/dovecot/conf.d/20-imap.conf with new version [....] Restarting IMAP/POP3 mail server: dovecotError: socket() failed: Address family not supported by protocol Error: service(imap-login): listen(::, 143) failed: Address family not supported by protocol Error: socket() failed: Address family not supported by protocol Error: service(imap-login): listen(::, 993) failed: Address family not supported by protocol Fatal: Failed to start listeners failed! invoke-rc.d: initscript dovecot, action "restart" failed. dpkg: error processing dovecot-imapd (--configure): subprocess installed post-installation script returned error exit status 1 Setting up dovecot-ldap (1:2.1.7-7) ...
These errors are caused by the lack of IPv6 support, which I mentioned in the previous tutorial. To remove the errors, open the main dovecot configuration file (/etc/dovecot/dovecot.conf) and find this line:
listen = *, ::
And change it to:
listen = *
The * means “all IPv4 addresses”, the :: means “all IPv6 addresses”. Now restart Dovecot, and you shouldn’t get any errors:
sudo service dovecot restart
Note: since I wrote this tutorial, there have been a few small changes to the default configuration file - you may find that the line is commented (with a # at the start of the line). If so, remember to uncomment it when you make your changes!
Tell Dovecot where your Mailbox is
Open /etc/dovecot/conf.d/10-mail.conf and find this line:
mail_location = mbox:~/mail:INBOX=/var/mail/%u
Change it to this:
mail_location = maildir:~/Maildir
Instruct Postfix to use Dovecot SASL
Now we need to tell Postfix that we would like to use Dovecot for SASL authentication. Open /etc/postfix/main.cf and add these lines:
smtpd_sasl_type = dovecot smtpd_sasl_path = private/auth smtpd_sasl_auth_enable = yes
Now tell Dovecot to listen for SASL authentication requests from Postfix. Open /etc/dovecot/conf.d/10-master.conf and comment out the current block that begins with service auth (place a # at the start of each line). Replace it with this:
service auth {
unix_listener /var/spool/postfix/private/auth {
mode = 0660
user = postfix
group = postfix
}
}
Now you want to enable plain text logins. Do it by adding these two lines to /etc/dovecot/conf.d/10-auth.conf. Make sure they are not already present in the file, or your settings may be overwritten with the default ones if the default is declared later in the file than the lines you add. If the parameters are already present, you can either modify the existing lines or comment them out and add these new ones:
disable_plaintext_auth = no auth_mechanisms = plain login
Note that although the logins are in plain text, we will be setting Postfix up later so that it only allows you to use plaintext logins from within SSL/TLS. This means that your login and password will sent in an encrypted session - you wouldn't see them in plain text if you used a packet sniffer, for example. For now, we’re allowing unencrypted plain text logins so that we can test logging in with Telnet. Since the connection is local (from the Pi to the Pi), your password isn’t being sent over any insecure networks so this is fine.
Testing SASL
Creating a new user for testing purposes is a good idea. Let’s call this temporary user testmail and give it the password test1234 Use this command to add the user, and follow the prompts including setting a password.
sudo adduser testmail
Now restart Postfix and Dovecot:
sudo service postfix restart sudo service dovecot restart
We’re now going to try and send an email after authenticating with SASL. The server is expecting to see a base64 encoded version of your username and password, so we have to convert it first. There are three ways of doing this, so I've given examples below using the testmail username and test1234 password:
#Method No.1
echo -ne '\000testmail\000test1234' | openssl base64
#Method No.2
perl -MMIME::Base64 -e 'print encode_base64("\0testmail\0test1234");'
#Method No.3
printf '\0%s\0%s' 'testmail' 'test1234' | openssl base64
I have discovered that if your password starts with a number, methods 1 and 2 don’t work. Assuming the username and password are testmail and test1234, the commands produce this:
AHRlc3RtYWlsAHRlc3QxMjM0
WARNING: If you’re having problems with authentication and you paste examples to forums or mailing lists, be aware that it is really easy to convert this back into your username and password (hence the creation of a test user). If you're using your real username and password to test, redact it before posting! Now, still logged into the Pi via SSH, you can telnet port 25 to test whether or not SASL is working. There’s only one extra step, which is the AUTH PLAIN command that comes after ehlo but before mail from. For testing, the permit_mynetworks parameter should be commented out under your postfix smtpd_recipient_restrictions block in /etc/postfix/main.cf. If you’re following on from Raspberry Pi Email Server Part 1: Postfix then this should already be the case. If you have to change it, remember to reload postfix (sudo service postfix reload) after you change the value. Here’s an example:
telnet localhost 25 Trying 127.0.0.1... Connected to localhost. Escape character is '^]'. 220 samhobbs ESMTP Postfix (Debian/GNU) ehlo facebook.com 250-samhobbs 250-PIPELINING 250-SIZE 10240000 250-VRFY 250-ETRN 250-STARTTLS 250-AUTH PLAIN LOGIN 250-ENHANCEDSTATUSCODES 250-8BITMIME 250 DSN AUTH PLAIN AHRlc3RtYWlsAHRlc3QxMjM0 235 2.7.0 Authentication successful mail from:testmail 250 2.1.0 Ok rcpt to:me@externalemail.com 250 2.1.5 Ok data 354 End data with. Subject: This is my first email that has been authenticated with Dovecot SASL Woop woop . 250 2.0.0 Ok: queued as B87133F768 quit 221 2.0.0 Bye Connection closed by foreign host.
Now try again but enter the username/password incorrectly (base64 encode something random) – you should get an error message and the email won’t send. If everything went to plan, then SASL is working properly! You can now uncomment permit_mynetworks again.
Separating Incoming email (unauthenticated) from Outgoing Email (SASL authenticated)
It’s probably a good idea to have a dedicated port for sending outgoing email…here’s why: Port 25 doesn’t require (but does offer) SSL/TLS encryption. If you mess up configuring your mail client you could end up letting it authenticate with SASL over insecure connections. Using a different port that only accepts SSL/TLS connections removes the risk that a poorly configured email client could be sending your password unencrypted over dodgy networks. There are two ports you can use for this:
- 465: SMTP over SSL
- 587: Email submission
587 is the “official” port for email clients (like K9 mail, Thunderbird and Outlook) to use when submitting messages to the Mail Submission Agent (your email server) – the submission may be encrypted or unencrypted depending on the server configuration. 465 was a port that was assigned for SMTP with SSL/TLS before the STARTTLS protocol was introduced, back in the days when you chose your port and that decided on the type of connection you were going to get (encrypted or unencrypted). STARTTLS changed things because it allows you to connect with an unencrypted connection (like the one you get with Telnet), and then upgrade to an encrypted connection without changing port… so when STARTTLS was introduced, SMTPS on port 465 was removed from the standard because you could do the same thing with a single port (25). However, I think there is some value in specifying a port for submission that only accepts SSL/TLS encrypted connections, and won’t work if the connection isn’t encrypted. This means that if you misconfigure your email client it just won’t work, instead of working and sending your password in an unencrypted format. So, anyway… Here’s how to set up Postfix to listen on port 465 for encrypted connections. The first step is telling Postfix to listen on port 465, so open /etc/postfix/master.cf and uncomment the line:
smtps inet n - - - - smtpd
Now restart Postfix:
sudo service postfix restart
Test whether Postfix is listening on port 465:
telnet localhost 465 Trying 127.0.0.1... Connected to localhost. Escape character is '^]'. 220 samhobbs.co.uk ESMTP Postfix (Debian/GNU) ehlo samhobbs.co.uk 250-samhobbs 250-PIPELINING 250-SIZE 10240000 250-VRFY 250-ETRN 250-STARTTLS 250-AUTH PLAIN LOGIN 250-ENHANCEDSTATUSCODES 250-8BITMIME 250 DSN quit 221 2.0.0 Bye Connection closed by foreign host.
OK, so now it’s listening on the right port, but it’s allowing unencrypted connections. Here’s how you force TLS on port 465: open /etc/postfix/master.cf and find the line you uncommented earlier. Below it are some options, you want to edit them so that they look like this (i.e. uncomment lines 2 and 3):
smtps inet n - - - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes
Line 3 is forcing TLS on port 465, and line 2 means that connections to port 465 have a different label in the logs, which can be useful for debugging.
sudo service postfix restart
Now try connecting with Telnet again… you should be able to establish a connection, but not receive any prompts from the server:
telnet localhost 465 Trying 127.0.0.1... Connected to localhost. Escape character is '^]'. exit exit Connection closed by foreign host.
Now try openssl:
openssl s_client -connect localhost:465 -quiet depth=0 CN = samhobbs verify error:num=18:self signed certificate verify return:1 depth=0 CN = samhobbs verify return:1 220 samhobbs.co.uk ESMTP Postfix (Debian/GNU) quit 221 2.0.0 Bye
Good: we are able to start a TLS encrypted connection. We got some errors because the certificate is self-signed (it's not signed by a certificate that is in the trusted root store on the server) but this is OK because we're just using the certificate for testing for now. When you come back later to set up a proper certificate, you can use this command to verify it. The -CApath option tells openssl where the trusted certificates are stored on your system:
openssl s_client -connect localhost:465 -quiet -CApath /etc/ssl/certs
Successful validation looks something like this:
sam@samhobbs:~$ openssl s_client -connect localhost:465 -quiet -CApath /etc/ssl/certs depth=3 C = SE, O = AddTrust AB, OU = AddTrust External TTP Network, CN = AddTrust External CA Root verify return:1 depth=2 C = GB, ST = Greater Manchester, L = Salford, O = COMODO CA Limited, CN = COMODO RSA Certification Authority verify return:1 depth=1 C = GB, ST = Greater Manchester, L = Salford, O = COMODO CA Limited, CN = COMODO RSA Domain Validation Secure Server CA verify return:1 depth=0 OU = Domain Control Validated, OU = PositiveSSL, CN = samhobbs.co.uk verify return:1 220 samhobbs.co.uk ESMTP Postfix (Ubuntu) quit 221 2.0.0 Bye
There are a couple more changes we want to make here: first, tell Postfix to only advertise SASL authentication over encrypted connections (so that you don’t accidentally send your password in the clear). Open /etc/postfix/main.cf and add this line:
smtpd_tls_auth_only = yes
sudo service postfix reload
Now connect to port 25 and you shouldn’t see AUTH advertised:
telnet localhost 25 Trying 127.0.0.1... Connected to localhost. Escape character is '^]'. 220 samhobbs.co.uk ESMTP Postfix (Debian/GNU) ehlo samhobbs.co.uk 250-samhobbs.co.uk 250-PIPELINING 250-SIZE 10240000 250-VRFY 250-ETRN 250-STARTTLS 250-ENHANCEDSTATUSCODES 250-8BITMIME 250 DSN
Lastly, we want to override the smtp_recipient_restrictions for port 465 so that it doesn't accept incoming messages from unauthenticated users. At first, I didn't make this change and I noticed that some spam emails were coming in on port 465 and bypassing my spam filter, which I configured to scan all incoming email on port 25, but not 465 because I only expected it to be used for outgoing email. We can do this by overriding the smtp_recipient_restrictions list for port 465 in /etc/postfix/master.cf. Open master.cf and find the smtps line. Add a new recipient restrictions list option like this:
smtps inet n - - - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes -o smtpd_recipient_restrictions=permit_sasl_authenticated,reject
Now reload postfix:
sudo service postfix reload
Perfect! Postfix configuration is now complete.
Testing IMAP
There are two main protocols for fetching mail: POP and IMAP. The main difference between them is what they do with emails when they collect them: a POP client will fetch email from your server and remove it from the server when it’s done. This is inconvenient if you want to connect with two or more devices (like a phone and a computer) and have complete copies of all your emails on both. IMAP, on the other hand, makes a copy of the emails on the server and leaves the originals there. For this reason, I think IMAP is much more useful than POP and I didn’t even bother to set up POP on my server. We can now test the IMAP server with Telnet in a similar way to SMTP & SASL testing earlier. This time, we’ll be using port 143, the standard port for IMAP. The stages are:
- establish a connection with
telnet localhost 143 - log in with
a login "USERNAME" "PASSWORD"" (not base64 encoded this time) - select inbox to see messages inside
b select inbox - logout with
c logout
In case you're wondering, the "a b c" thing is done because a client can send multiple commands to the server at once, and they might not come back in the same order depending on what they are. So, the responses have the same letter as the commands they are responding to so that the client doesn't get muddled. Here’s an example, using the testmail user we created earlier:
telnet localhost 143 Trying 127.0.0.1... Connected to localhost. Escape character is '^]'. * OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE STARTTLS AUTH=PLAIN AUTH=LOGIN] Dovecot ready. a login "testmail" "test1234" a OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE SORT SORT=DISPLAY THREAD=REFERENCES THREAD=REFS MULTIAPPEND UNSELECT CHILDREN NAMESPACE UIDPLUS LIST-EXTENDED I18NLEVEL=1 CONDSTORE QRESYNC ESEARCH ESORT SEARCHRES WITHIN CONTEXT=SEARCH LIST-STATUS SPECIAL-USE] Logged in b select inbox * FLAGS (\Answered \Flagged \Deleted \Seen \Draft) * OK [PERMANENTFLAGS (\Answered \Flagged \Deleted \Seen \Draft \*)] Flags permitted. * 1 EXISTS * 0 RECENT * OK [UNSEEN 1] First unseen. * OK [UIDVALIDITY 1385217480] UIDs valid * OK [UIDNEXT 2] Predicted next UID * OK [NOMODSEQ] No permanent modsequences b OK [READ-WRITE] Select completed. c logout * BYE Logging out c OK Logout completed. Connection closed by foreign host.
Adding TLS support
Now that we know IMAP is working, we need to enable IMAPS (imap with SSL/TLS). The standard port for this is 993. Many other tutorials that were written for older versions of dovecot will tell you to do this in different ways that won’t work, I tried 3 different methods before I ended up with a working one. First, edit /etc/dovecot/conf.d/10-master.conf, find the “service imap-login” block and uncomment the port and SSL lines so that it looks like this:
service imap-login {
inet_listener imap {
port = 143
}
inet_listener imaps {
port = 993
ssl = yes
}
}
Edit 14/10/2015: the default dovecot configuration files changed recently after Jessie became the new stable distribution of Debian, which caused some users problems; TLS on port 993 used to be enabled by default but now it isn't. We need to re-enable it. In /etc/dovecot/conf.d/10-ssl.conf, find ssl = no and change it to:
ssl = yes
There have been some security vulnerabilities discovered in older versions of the SSL protocol in recent times. SSLv2 is disabled by default, but it doesn't harm to explicitly disable it again. SSLv3 is vulnerable to an attack called POODLE, so we will disable it too. In the same file, find the ssl_protocols parameter line, uncomment it and add !SSLv3 to the end, like this:
ssl_protocols = !SSLv2 !SSLv3
Edit 02/09/2017: if you're using Debian Stretch or later, or one of its derivatives, then you will need to edit that line to match the following. The SSLv2 option is no longer recognised as an option for ssl_protocols because it has been removed entirely:
ssl_protocols = !SSLv3
For some bizarre reason, the Dovecot package for Raspberry Pi (and possibly newer versions of Ubuntu) does not create a self-signed certificate during installation like it used to. So, we have to create one manually. If you look in /usr/share/dovecot/ you will find the script that used to be used to generate the certificate; we can use it ourselves to simplify the process. The script is located at /usr/share/dovecot/mkcert.sh and looks like this:
#!/bin/sh
# Generates a self-signed certificate.
# Edit dovecot-openssl.cnf before running this.
OPENSSL=${OPENSSL-openssl}
SSLDIR=${SSLDIR-/etc/ssl}
OPENSSLCONFIG=${OPENSSLCONFIG-dovecot-openssl.cnf}
CERTDIR=/etc/dovecot
KEYDIR=/etc/dovecot/private
CERTFILE=$CERTDIR/dovecot.pem
KEYFILE=$KEYDIR/dovecot.pem
if [ ! -d $CERTDIR ]; then
echo "$SSLDIR/certs directory doesn't exist"
exit 1
fi
if [ ! -d $KEYDIR ]; then
echo "$SSLDIR/private directory doesn't exist"
exit 1
fi
if [ -f $CERTFILE ]; then
echo "$CERTFILE already exists, won't overwrite"
exit 1
fi
if [ -f $KEYFILE ]; then
echo "$KEYFILE already exists, won't overwrite"
exit 1
fi
$OPENSSL req -new -x509 -nodes -config $OPENSSLCONFIG -out $CERTFILE -keyout $KEYFILE -days 365 || exit 2
chmod 0600 $KEYFILE
echo
$OPENSSL x509 -subject -fingerprint -noout -in $CERTFILE || exit 2
If you were going to use this certificate for any significant length of time, it would be worth editing the parameters in the config file it uses (/usr/share/dovecot/dovecot-openssl.cnf) to set the proper common name and contact details on the certificate. However, I suggest you leave the defaults as they are, use this certificate just for testing, and then come back later and generate a new cert when everything is working (more on that later). You must be in the same folder as the configuration file when you run the script, or it will not find the config and the certificate generation will fail. The following two commands will change to the right folder and then execute the script:
cd /usr/share/dovecot sudo ./mkcert.sh
You should see a message "writing new private key to '/etc/dovecot/private/dovecot.pem'" and then some details about the certificate. Next, find the following two lines in /etc/dovecot/conf.d/10-ssl.conf and uncomment them:
#ssl_cert = </etc/dovecot/dovecot.pem #ssl_key = </etc/dovecot/private/dovecot.pem
Now reload dovecot to apply the changes:
sudo service dovecot reload
Since IMAPS is a connection over SSL/TLS, we can’t use Telnet to test it. Instead, we use openssl to create a secure connection. There are two versions of the command, one will show you LOADS of information about the certificate used to encrypt the connection, and the other will suppress this info. I recommend trying the long version out of interest, but both will work the same for the test: For full information:
openssl s_client -connect localhost:993
For minimal information:
openssl s_client -connect localhost:993 -quiet
I won’t print the output of the first command, because it’s ridiculously long. Here’s an example of the second, including a login test:
admin@samhobbs /etc/dovecot/conf.d $ openssl s_client -connect localhost:993 -quiet depth=0 O = Dovecot mail server, OU = samhobbs, CN = samhobbs, emailAddress = root@samhobbs.co.uk verify error:num=18:self signed certificate verify return:1 depth=0 O = Dovecot mail server, OU = samhobbs, CN = samhobbs, emailAddress = root@samhobbs.co.uk verify return:1 * OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE AUTH=PLAIN AUTH=LOGIN] Dovecot ready. a login "testmail" "test1234" a OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE SORT SORT=DISPLAY THREAD=REFERENCES THREAD=REFS MULTIAPPEND UNSELECT CHILDREN NAMESPACE UIDPLUS LIST-EXTENDED I18NLEVEL=1 CONDSTORE QRESYNC ESEARCH ESORT SEARCHRES WITHIN CONTEXT=SEARCH LIST-STATUS SPECIAL-USE] Logged in b logout * BYE Logging out b OK Logout completed. Connection closed by foreign host.
Good stuff: SSL/TLS is working on port 993, and you can log in successfully. Note that by default Dovecot uses a “snakeoil” self-signed certificate. SSL/TLS certificates are used for two purposes: encryption and verification. The “snakeoil” certificate will encrypt your content but it won’t verify that you’re talking to your server – you could be talking to someone imitating your server (anyone can create a self-signed certificate claiming to be any website). If you’d like to get your certificate signed without forking out loads of money to a cert signing authority, I’d recommend CAcert. I've written a tutorial explaining how to generate your own cert and get it signed here. If you opt for a commercial certificate, you can use the CAcert tutorial to generate the certificate and then this tutorial will explain the differences in the installation/configuration of commercial certificates once you have it signed. If you're testing a proper certificate, use this command to tell openssl where the trusted root certificates are stored:
openssl s_client -connect localhost:993 -quiet -CApath /etc/ssl/certs
Tidying up and enabling WAN access
Before opening the ports on your router to the world, it’s a good idea to delete that test user because the password is so easy to guess.
sudo userdel testmail
Also, if you still use the "pi" login, for goodness' sake change the password from "raspberry"! You can do this using the passwd command when logged in as pi:
passwd
Or you can achieve the same thing when logged in as another user by using sudo to gain root privileges:
sudo passwd pi
Now you can open a few ports on your router’s firewall. Make sure your Pi has a static LAN IP address and then forward these ports from WAN to its LAN IP address:
- Port 25 for SMTP (used for receiving emails)
- Port 465 for secure SMTP (used for sending emails after SASL authentication)
- Port 993 for IMAPS (used to receive emails on your phone/tablet/computer)
Here’s an example on my router, running OpenWrt: 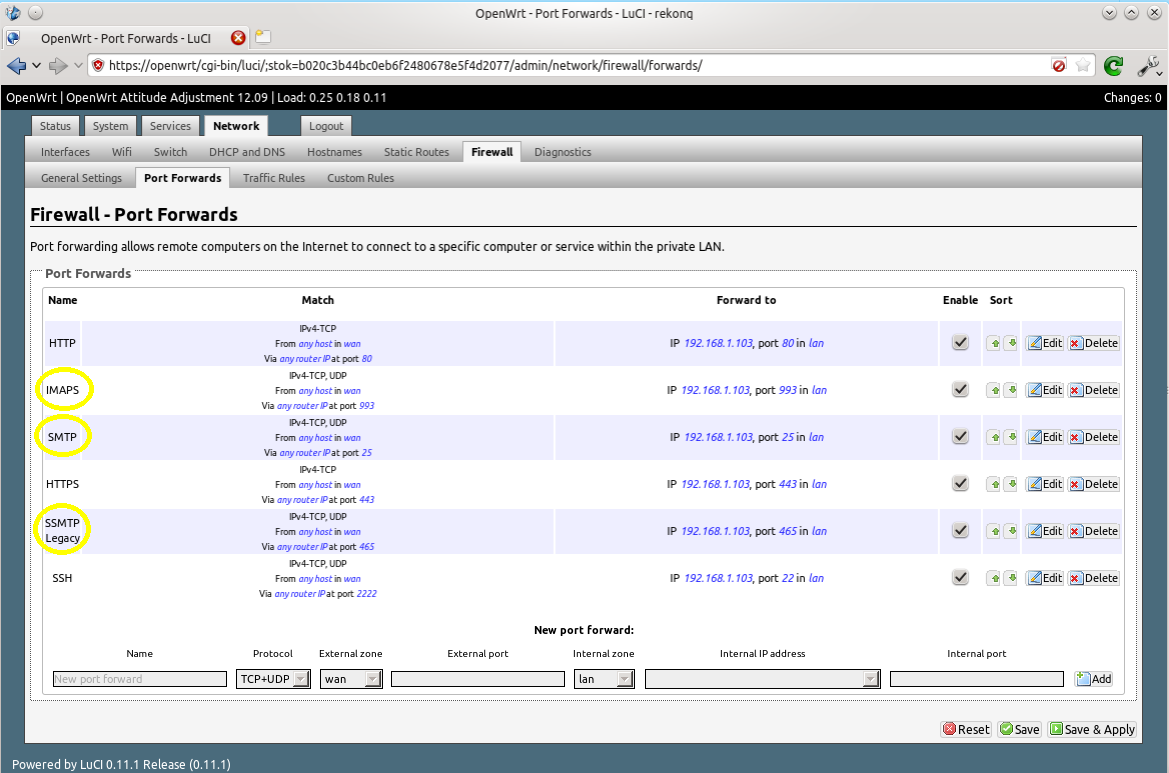
Setting up IMAP Email Clients
I’m now going to run through setting up IMAP email clients quickly, using K9 Mail on Android and Thunderbird on GNU/Linux as examples. The setup for Thunderbird on Windows and Mac OSX should be very similar. The basics are this:
- Select an IMAP connection
- Your login is your username only (omit @yourdomain.com), and you password is…your password!
- For incoming emails: select use SSL/TLS always and the program should automatically select port 993
- For outgoing emails: select SSL/TLS always. The program may suggest port 587, but you want port 465
K9 Mail
Open K9 Mail and select add new account. Type in your account information (you@yourdomain.com and password) and then select manual setup. Select IMAP and then enter your information as follows… Incoming email: 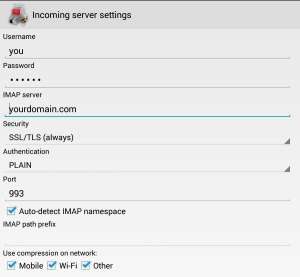 Outgoing email:
Outgoing email: 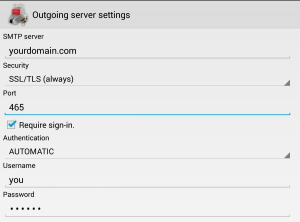
Thunderbird
Open Thunderbird, and then click Account Actions –> Add Mail Account. Fill in your password and email address, which is your username followed by your fully qualified domain name (FQDN), i.e. username@yourdomain.com: 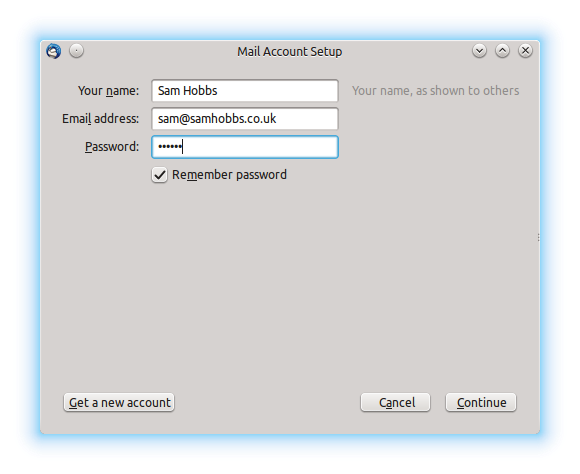 Thunderbird will try to auto-detect settings and fail. Don’t worry, this is normal. Select “manual config”:
Thunderbird will try to auto-detect settings and fail. Don’t worry, this is normal. Select “manual config”: 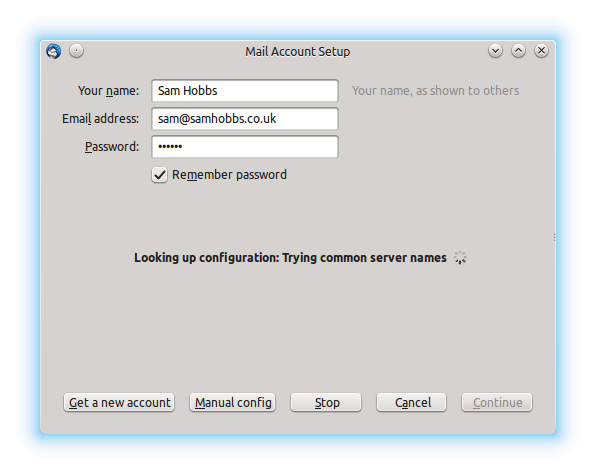 Now edit the settings as appropriate. I had to remove a period (.) from in front of my “server hostname”, and edit the SSL and Authentication settings. If you select “SSL/TLS” for both incoming and outgoing, ports 993 and 465 are automatically selected:
Now edit the settings as appropriate. I had to remove a period (.) from in front of my “server hostname”, and edit the SSL and Authentication settings. If you select “SSL/TLS” for both incoming and outgoing, ports 993 and 465 are automatically selected: 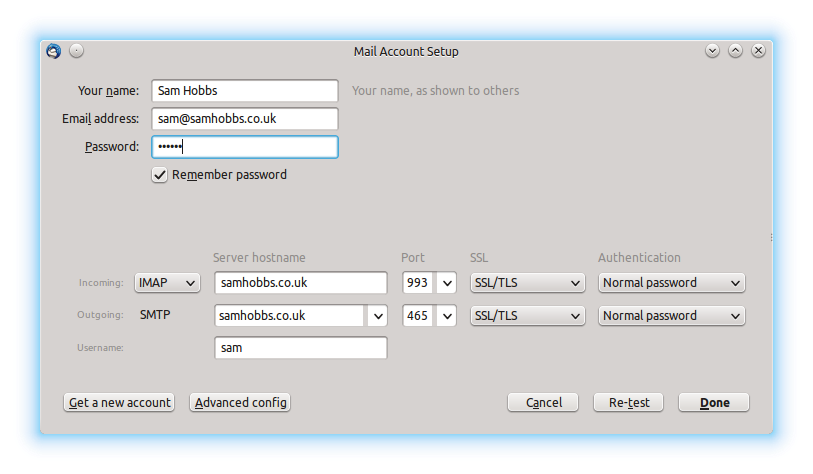 Now try emailing yourself from your external email address, and see if your email gets through. If you are having problems, be sure to check you’ve set up an MX record as well as a DNS A record.
Now try emailing yourself from your external email address, and see if your email gets through. If you are having problems, be sure to check you’ve set up an MX record as well as a DNS A record.
Stuck in spam filters?
A few people have contacted me recently to say that their email server is working fine but their emails are getting sent to Gmail's spam folder. If you are experiencing problems like this (or even if you're not), try setting up an SPF and/or PTR record as explained in my DNS basics tutorial. You might also want to check if your domain name or IP address are on any blacklists. There's a handy website called MX toolbox that lets you do this (choose blacklist check from the dropdown menu).
Almost done…
Good news! If you’ve reached this far and everything is working, then you’re almost done. The next step (Webmail with Squirrelmail) is optional but by far the easiest of the three steps. If you’ve hit a rut, please post a comment and I’ll try and help you out. If not… continue to Raspberry Pi Email Server Part 3: Squirrelmail
Comments
Dovecot can't read your
SSL key Path
in /etc/dovecot/conf.d/10-ssl.conf
uncomment the ssl_cert and ssl_key lines.
Thank you, tutorial updated
SSL in 143
Sam,Dax,
Thanks, worked a treat.
I'll continue on.
Regards
Mark
Postfix Port 465
Hey,
in advance, very good instructions here.
I am getting the same error over and over again when trying to connect on port 465 after enabling tls:
CONNECTED(00000003)
3069240528:error:140790E5:SSL routines:SSL23_WRITE:ssl handshake failure:s23_lib.c:184:
---
no peer certificate available
---
No client certificate CA names sent
---
SSL handshake has read 0 bytes and written 295 bytes
---
New, (NONE), Cipher is (NONE)
Secure Renegotiation IS NOT supported
Compression: NONE
Expansion: NONE
---
any suggestions for resolving this ??
certificate might not exist
/etc/postfix/main.cfto see which certificates are specified (if any). You're looking for lines like this: If they're commented, uncomment them and restart dovecot then try again. If they're uncommented and it still doesn't work, verify that they exist. Let me know how you get on! SamAuthentication failed
Hi Sam,
so i get pretty far, i can even send emails to the user (i can see that a new file in ~/Maildir/new/ is created). But something with the imap authentication goes wrong. I added a username,-password to openssl via
>>>>>>>>>>>>>>>>>>>>>>>>>>>
echo -ne '\000testmailxxx\000test1234xxx' | openssl base64
<<<<<<<<<<<<<<<<<<<<<<<<<<<
Regards, Stephan
but accessing the imap acount for testmailxxx still fails:
>>>>>>>>>>>>>>>>>>>>>>>>>>>
~ $ telnet localhost 143
Trying ::1...
Trying 127.0.0.1...
Connected to localhost.
Escape character is '^]'.
* OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE AUTH=PLAIN AUTH=LOGIN] Dovecot ready.
a login "testmailx" "test1234xxx"
a NO [AUTHENTICATIONFAILED] Authentication failed.
<<<<<<<<<<<<<<<<<<<<<<<<<<<
wrong username?
i redacted some information
i redacted some information so that's not it :-(
So everything that is neccessary to create a new emailaccount should be to create a new user acount (e.g. sudo adduser joe.someone) and than add that username together with a password to openssl via
printf '\0%s\0%s' 'joe.someone' 'somePA55w0rd' | openssl base64
?!
base64 encoding not necessary for IMAP
Recieving mail
Hey sam, great tutorial!
Though i do have one problem.
I can't seem to recieve mail on my client.
The mail is recieved in the Maildir/new map, but it won't send it to Outlook.
I hope you could help me somehow.
Thanks!
TLS support?
Recieve mail
Hey sam, thanks for responding so fast.
I can indeed send mail to others. However when someone sends an email to me, the message will save in /home/USER/Maildir/new but won't appear in my mail client.
I tried this in outlook, android mail and ios mail but none will recieve mail.
Thanks for the help!
A couple of things to check:
Things to check
I did forward the right ports.
Sadly i don't quite know how to do a manual openssl s_client test, i'm pretty new to the whole RasPi/linux thing.
The thing is, it suddenly works now.
Yesterday I installed RoundCube instead of Squirrelmail (I prefer the RoundCube UI) and it kept giving me an error about the Maildir not existing.
So i played a bit with the mail_location in the 10_mail.conf file, but nothing worked.
However, I just powered up my Pi and suddenly it works, all the mail is in the RoundCube inbox but i have no clue why it does work now.
Either way, thanks for the quick response and for the great tutorial!
Glad you got it working.
openssl s_client. SamOne more question
Ah i forgot about that, sorry.
I do have one more question.
Is there a way to add a user that is not able to login to my ssh/remote desktop?
Because the way you described with the testmail account, also made it possible to login over ssh/remote desktop.
Rutger
nologin
/home/user/.ssh/authorized_keys(server preparation). Using publickey authentication protects against bots brute forcing SSH passwords. But to answer your question directly, open/etc/passwd: find the line for the user you want to prevent logging in, which probably looks something like this: Change the last field, which is the login shell, to/usr/sbin/nologin: This will always return false if someone tries to log in to that account (i.e. access will be denied). SamThanks
Thanks for everything, it works great :)
Once more, thanks for the great tutorial!
Telnet to port 465 does not work
Sam,
Thank you for providing such a thorough tutorial on setting up email! I'm working on my second email server now :-). I've hit a puzzle though. Everything is working, I can send and receive email using K-9 and through squirrelmail. The problem is I cannot send e-mail from within my domain. If I do a telnet to port 465 from the localhost I get the usual telnet prompt without the line that shows "220 samhobbs ESMTP Postfix (Debian/GNU)" (from your example). If I type ehlo thegilmanexperiment.net the connection is immediately closed. I feel like I have missed some configuration somewhere. I am using Raspbian build 5/5/2015. I also noticed that I do not have the mkcert.sh file that you talked about. This was not a problem, it seems there was already a self-signed certificate.
Any help on resolving the telnet to port 465 would be greatly appreciated.
Thanks!
-Keith
use openssl s_client for port 465
openssl s_client, nottelnet. Samuse openssl s_client for port 465
Hi Sam,
Thanks for your response! I found the problem. I was trying to send email from a local (on my network) client which uses port 25. The problem was my postfix main.cf file, specifically the mynetworks line. The original line was:
mynetworks = 127.0.0.0/8 [::ffff:127.0.0.0]/104 [::1]/128
I changed this to
mynetworks = 127.0.0.0/8 192.0.0.0/8
And that solved the problem. I am a little confused about an error in the mail.log file as I was working on this. I originally tried 192.168.0.0/8 but got a warning that I should use 192.0.0.0. Doesn't the /8 specify a mask for the last 8 bits?
Thanks again!!
-Keith
cannot select "inbox"
Hi Sam, great tutorials, I've been trying to folllow them over the past few days with moderate success. most errors I've been able to "solve". I'm stuck however on trying to enter "b select inbox". I get the error:
b NO [SERVERBUG] Internal error occurred. Refer to server log for more information. [2015-11-22 11:19:20]
i'm not sure why this is?
Two reasons spring to mind:
/etc/skelbefore adding a new user) or you might have missed the bit at the start of part 1 where you changehome_mailboxto Maildir. SamHi Sam,
Hi Sam,
thank's for your feedback. I looked into both of your suggestions and double checked it and the folders seem to exist there:
pi@raspberrypi ~ $ sudo ls -a /etc/skel/Maildir
. .. cur .Drafts new .Sent .Spam .Templates tmp .Trash
pi@raspberrypi ~ $ sudo ls -a /home/testmail/Maildir/
. .. cur .Drafts new .Sent .Spam .Templates tmp .Trash
I also set the home_mailbox to maildir in the postfix main.cf file so i'm kinda stumped.
I even deleted the user, deleted the folders (rm -rf) and readded the user but still no joy. how do I check the server log? Maybe we can find out what's wrong in there.
log files
/var/log/mail.loghas everything and/var/log/mail.errjust has the errors. They are both text files, so you can use lots of utilities to read them. If you just want to read the end, do: If you want to see the log update as new stuff happens, do: (and ctrl+C to exit). To read the whole thing, try: ctrl+G to go the end, b to move back a page, space to move forward a page. The following command opens the log in less but also updates as new data is written. SamHi Sam,
Hi Sam,
Thank's for that, I ran the sequence again and printed out the log. I think this is the important part:
Nov 22 17:55:31 raspberrypi dovecot: imap-login: Login: user=, method=PLAIN, rip=127.0.0.1, lip=127.0.0.1, mpid=7405, secured, session=
Nov 22 17:55:38 raspberrypi dovecot: imap(testmail): Error: open(/var/mail/testmail) failed: Permission denied (euid=1001(testmail) egid=1001(testmail) missing +w perm: /var/mail, we're not in group 8(mail), dir owned by 0:8 mode=0775)
Nov 22 17:55:38 raspberrypi dovecot: imap(testmail): Error: Failed to autocreate mailbox INBOX: Internal error occurred. Refer to server log for more information. [2015-11-22 17:55:38]
Nov 22 17:55:42 raspberrypi dovecot: imap(testmail): Disconnected: Logged out in=24 out=502
It looks like there are permission issues?
tell dovecot where you mailbox is
home_mailboxissue I was talking about earlier. I think you've missed the first part of tutorial 2, under "tell dovecot where your mailbox is". I should have realised it would be a Dovecot configuration error not Postfix, since Dovecot handles IMAP. SamYes you were right! It seems
Yes you were right! It seems in the conf file
mail_location = mbox:~/mail:INBOX=/var/mail/%u
appears twice and I only saw it in the first one, and the second one existed after the change I made.
Quick question, for every recipient that I would like to have on my domain, do they each need their own user account on the pi? Thanks again!
/etc/aliases
/etc/aliases, put your aliases in like this: Then run: to make the changes take effect. You may also have tosudo service postfix reload, and email to those aliases should go to your username's maildir (where you could sort it into folders with sieve scripts if you like). SamAdd new comment