Shellshock BASH probe alert using Fail2ban
"Shellshock" is the nickname for a recently discovered vulnerability in GNU BASH (Bourne-Again SHell) that has the potential to allow an attacker to execute arbitrary commands through carefully crafted environment variables (see CVE-2014-6271). This is bad for desktop users, but far worse for servers because it's possible to exploit this vulnerability by attacking CGI scripts. The CGI script doesn't even have to be written in BASH; on distributions that use BASH as the default shell, the environment variables will be passed to BASH before any CGI script is executed. Luckily, the default shell in Debian is DASH, which limits the problem for Debian derivatives like Ubuntu and Raspbian. If you run a Linux or UNIX-like system that uses BASH, you should update to the new patched version now. In fact, most Linux users probably updated before they even realised anything was wrong, since the patched version was available in the repositories very quickly. Meanwhile, Mac users were still waiting for Apple to comment... lol.

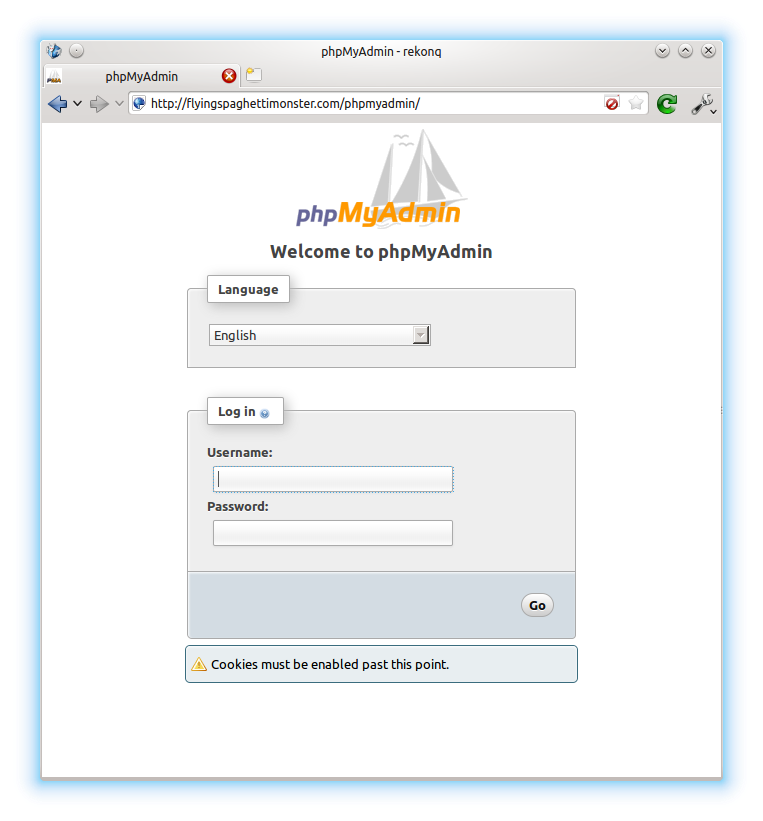 I recently installed a plugin for WordPress called “Better WP Security”. One of the features this plugin has is the ability to log all 404 errors, and temporarily or permanently block hosts that request too many non-existent pages in a short space of time. This is useful for blocking scripts that try to guess the location of your admin pages and then brute force their way in or exploit some specific vulnerability in the software. I noticed in the logs that one particular script (“w00tw00t.at.blackhats.romanian.anti-sec:)”) was checking my website to see if phpmyadmin had been installed but the setup script not run, requesting lots of pages like “phpMyAdmin/scripts/setup.php”. This got me thinking about securing the phpMyAdmin page a little, as I had pretty much just set it up and forgotten about it. I very rarely use it, but still wanted it installed just in case. So, the best solution was to simply disable access from outside my LAN.
I recently installed a plugin for WordPress called “Better WP Security”. One of the features this plugin has is the ability to log all 404 errors, and temporarily or permanently block hosts that request too many non-existent pages in a short space of time. This is useful for blocking scripts that try to guess the location of your admin pages and then brute force their way in or exploit some specific vulnerability in the software. I noticed in the logs that one particular script (“w00tw00t.at.blackhats.romanian.anti-sec:)”) was checking my website to see if phpmyadmin had been installed but the setup script not run, requesting lots of pages like “phpMyAdmin/scripts/setup.php”. This got me thinking about securing the phpMyAdmin page a little, as I had pretty much just set it up and forgotten about it. I very rarely use it, but still wanted it installed just in case. So, the best solution was to simply disable access from outside my LAN.