Restrict Access to phpMyAdmin from WAN
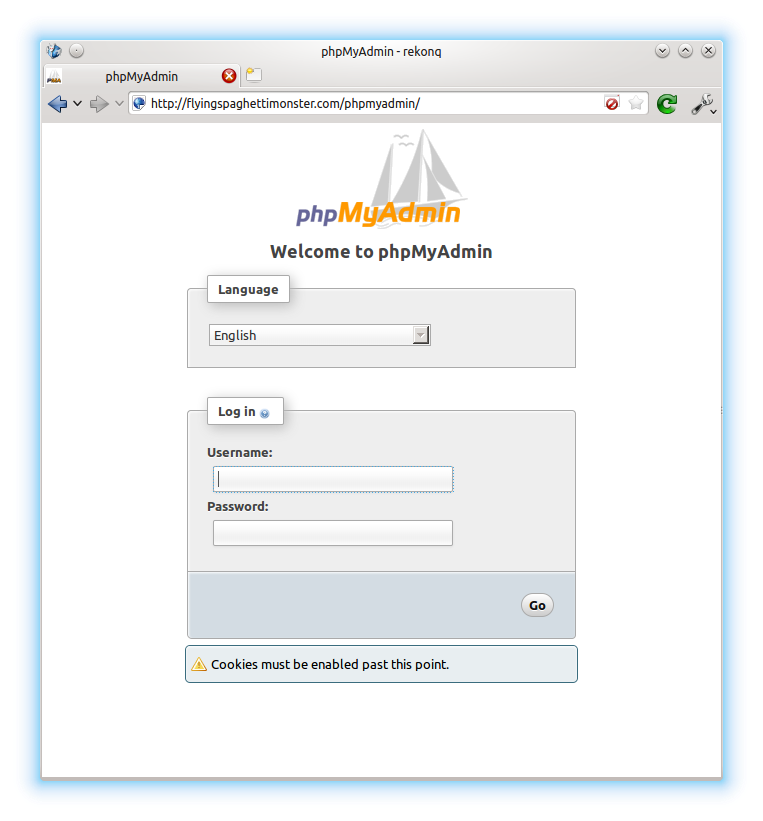 I recently installed a plugin for WordPress called “Better WP Security”. One of the features this plugin has is the ability to log all 404 errors, and temporarily or permanently block hosts that request too many non-existent pages in a short space of time. This is useful for blocking scripts that try to guess the location of your admin pages and then brute force their way in or exploit some specific vulnerability in the software. I noticed in the logs that one particular script (“w00tw00t.at.blackhats.romanian.anti-sec:)”) was checking my website to see if phpmyadmin had been installed but the setup script not run, requesting lots of pages like “phpMyAdmin/scripts/setup.php”. This got me thinking about securing the phpMyAdmin page a little, as I had pretty much just set it up and forgotten about it. I very rarely use it, but still wanted it installed just in case. So, the best solution was to simply disable access from outside my LAN.
I recently installed a plugin for WordPress called “Better WP Security”. One of the features this plugin has is the ability to log all 404 errors, and temporarily or permanently block hosts that request too many non-existent pages in a short space of time. This is useful for blocking scripts that try to guess the location of your admin pages and then brute force their way in or exploit some specific vulnerability in the software. I noticed in the logs that one particular script (“w00tw00t.at.blackhats.romanian.anti-sec:)”) was checking my website to see if phpmyadmin had been installed but the setup script not run, requesting lots of pages like “phpMyAdmin/scripts/setup.php”. This got me thinking about securing the phpMyAdmin page a little, as I had pretty much just set it up and forgotten about it. I very rarely use it, but still wanted it installed just in case. So, the best solution was to simply disable access from outside my LAN.
 OwnCloud is a free (libre), open source equivalent to DropBox. As well as the program you install on your server, it has free desktop sync clients for Linux, Windows and Mac, and apps for Android and iOS. I’m just going to cover the server side of things for your Pi in this tutorial, because the desktop client can be found in the Ubuntu repos, and the app is on the Play Store. If you want the Android app free of charge, then install it via
OwnCloud is a free (libre), open source equivalent to DropBox. As well as the program you install on your server, it has free desktop sync clients for Linux, Windows and Mac, and apps for Android and iOS. I’m just going to cover the server side of things for your Pi in this tutorial, because the desktop client can be found in the Ubuntu repos, and the app is on the Play Store. If you want the Android app free of charge, then install it via