 If you run your own website, email server or other services like OwnCloud at home then you may find yourself in need of a SSL certificate. When you install Apache, it generates a self-signed "snakeoil" certificate that can be used to encrypt your session. However, while this certificate is useful for testing purposes, it falls short in a couple of important ways:
If you run your own website, email server or other services like OwnCloud at home then you may find yourself in need of a SSL certificate. When you install Apache, it generates a self-signed "snakeoil" certificate that can be used to encrypt your session. However, while this certificate is useful for testing purposes, it falls short in a couple of important ways:
- The snakeoil certificate has not been signed by an authority that your browser trusts, so your browser will throw an error when you connect.
- The common name on the certificate probably doesn't match your domain name. Another browser error.
- Short of manually inspecting the certificate's checksum, you have no guarantee that you are communicating with your own server - it could easily be an imposter using another self-signed certificate.
This tutorial will show you how to generate your own SSL certificate, and get it signed by the community driven SSL certificate signing authority CAcert. Once you have imported the certificate into your browser or into your operating system's root filesystem, your computer will automatically verify the identity of the server and you will enjoy error-free secure communications. Oh, and CAcert is free of charge!
Before we start: a quick note about filename extensions
As far as I can tell, Linux is not at all bothered about what you name your certificate and certificate key files. You could use the .magic extension for your cert if you liked and it would probably still work. From what I've read, file name extensions seem to only matter on Windows, whereas on Linux they're just descriptive. However, it's probably worth noting that there are lots of different types of certificate encoding styles, which have been summarised neatly here. Some extensions such as .pem and .der imply that the file is encoded in a certain way. Since we are able to choose whatever extension we like, I've chosen the following:
- .csr for the certificate signing request (CSR)
- .crt for the signed certificate file
- .key for the key file
These have the benefit of not implying any particular encoding. The first time I did this on my Pi, I used .pem for everything and got in a muddle, forgetting which file was which. This should make things much easier!
Generate your certificate
We are going to use a two step process to generate your certificate. First, run this command, which will generate a private key:
openssl genrsa -out <filename for your private key>.key 4096
Now we will generate a new certificate signing request (CSR) from your private key:
openssl req -new -key <filename for your private key>.key -out <filename for the CSR>.csr
This stage requires user input, a series of questions about what information you would like to be on the certificate. Since CAcert is an automated service, it discards most of the information on the certificate (so that it doesn't certify the information it is unable to verify), leaving only the essentials: the email address and the common name. Here is the information you will be asked for:
- Country Name (use a two letter code e.g. GB)
- State or Province Name (e.g. Surrey)
- Locality Name (e.g. Guildford)
- Organisational Name (e.g. Sam Hobbs' Personal Website)
- Organisational Unit Name (e.g. Website)
- Common Name (your domain name - see note below - e.g. samhobbs.co.uk)
- Email Address (the contact address for your administrator e.g. webmaster@samhobbs.co.uk)
Don't set a password - leave it blank when asked. We will keep the key file private by setting appropriate permissions. The common name is important here: most websites rewrite https:// to https://www. or vice versa. If your website is available at https://yourdomain.com then you should use yourdomain.com as the common name; if your website is at https://www.yourdomain.com then your common name should be www.yourdomain.com or *.yourdomain.com (the wildcard will match any subdomain, meaning you can use the same cert for https://mail.yourdomain.com and https://www.yourdomain.com, which is handy). Personally, I use a wildcard certificate. If you were paying for a normal certificate authority to sign your certificate then a wildcard cert would be more expensive, but CAcert is of course free so you might as well take advantage of it!
Install the CAcert root certificate
Every operating system comes pre-loaded with a set of certificates that are seen as trusted by the OS. This includes certificates from verisign and other big name certificate signing authorities. Very few OSes trust CAcert by default, although a couple of Linux distributions do. The CAcert website provides https using a certificate that was signed by the CAcert root. Since you are going to be sending sensitive information to the website during registration, it makes sense to install the CAcert root certificate now so that you can use the site without browser errors. To install the CAcert root certificate from the commandline, you can use these commands:
cd ~ wget http://www.cacert.org/certs/root.txt sudo cp root.txt /etc/ssl/certs/cacert-root.crt
Those commands will download the CAcert root certificate into your home directory, and then copy it to your certificates folder. If you look in your certs directory (ls -l /etc/ssl/certs) you will see that all of the certs have sensible certificate names like GeoTrust_Global_CA.pem, but there are also a load of symbolic links with names like 2c543cd1.0 that point to the certificate files with the human readable names. Those symlink names like 2c543cd1.0 are hashes of the certificate files, and are there to enable programs on your computer to quickly check whether the root certificate is in your computer's certificate directory or not. Some programs manage to recognise that the certificate is installed just fine without the symlinks, but some of them do not. Openssl is one of the ones that doesn't. So, we need to make use of one more command to create a symlink for the newly installed cacert-root.crt (this will also refresh the symlinks for the rest of the certs in the folder):
sudo c_rehash /etc/ssl/certs
Now that the CAcert root cert is installed, almost all software on your system will recognise it (chromium, rekonq etc.). The exception to this is Mozilla software such as the Firefox web browser and Thunderbird email client. Mozilla software has its own certificate database, which has both advantages and disadvantages. For example, if you're using a system where you don't have admin rights, you can still easily import the CAcert root to Firefox. The disadvantage is that if you are an administrator, you can't do a one-stop installation: you have to import it separately to Firefox. To install the certs, open Firefox and navigate to the root certificate downloads page and click on the links for the class 1 and class 3 .pem encoded root certificates. You will be prompted to decide whether to import them or not. To install to Android, follow this tutorial of mine.
Required Email Address
CAcert verifies that you own the domain it is signing a certificate for by sending a verification link to one of the following email addresses:
- root@yourdomain.com
- webmaster@yourdomain.com
- postmaster@yourdomain.com
You therefore need to be able to receive email to one of these addresses. You can set up your own email server, or failing that some domain name registrars provide email forwarding capabilities. If you used my tutorials to set up your email server then you may want to add some aliases to your server so that emails to those addresses above are delivered to your username. Here's how: Edit /etc/aliases and add:
postmaster: yourusername webmaster: yourusername root: yourusername
Now run this command to load the new aliases:
sudo newaliases
And reload Postfix:
sudo service postfix reload
Submitting the CSR to CAcert
First things first, you will need to go to the CAcert website and create an account: Please note that CAcert has signed its own SSL certificate, so your browser may throw an error if you haven't imported the root cert yet. 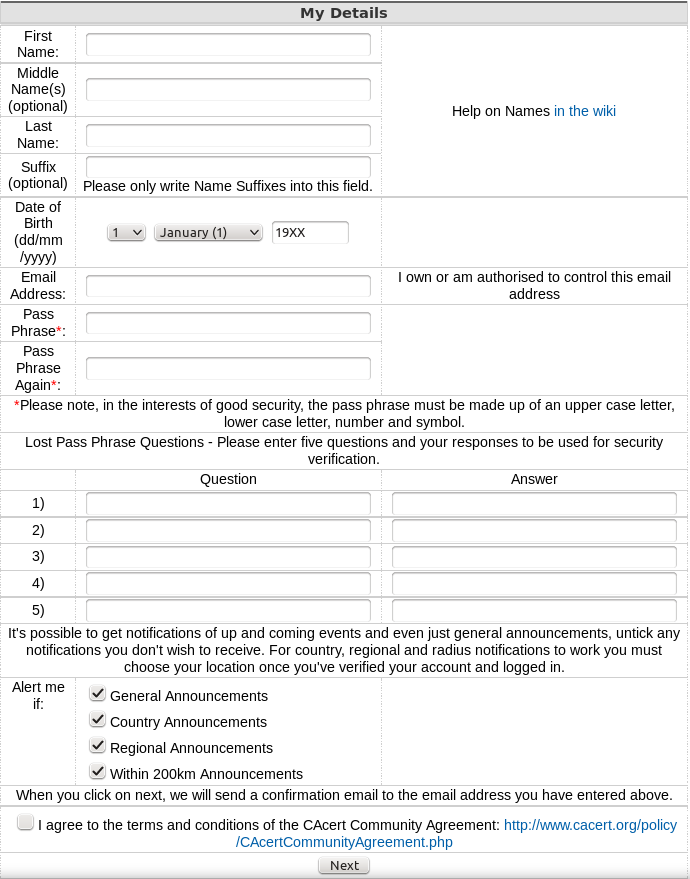 After you have created your account and logged in, navigate to server certificates --> new. On your server, use
After you have created your account and logged in, navigate to server certificates --> new. On your server, use cat to print the the Certificate Signing Request (CSR) you created earlier and then copy & paste it into the box:
cat <filename for the CSR>.csr
...and click submit. The result will be displayed on screen, and you will also be emailed the certificate. Copy and paste it into a file with the .crt extension, e.g. using nano:
sudo nano <path to your cert>.crt
...then CTRL+SHIFT+V to paste, CTRL+X, save when prompted. Note: the BEGIN CERTIFICATE and END CERTIFICATE lines are part of the cert, so copy those too!
Certificate File Locations
Assuming your certificates and key file are in your home directory, it's a good idea to move them to the proper locations
- Your key file should be stored at
/etc/ssl/private/samhobbs.key. - Your certificate file should be stored at
/etc/ssl/certs/samhobbs.crt. - You can get rid of your CSR, or keep it for reference if you like.
Permissions & Ownership
Your key file is secret. It should be owned by root, and your permissions should be set so that only the root user can read and write to it. This command will set it to be owned by root:
sudo chown root:root /etc/ssl/private/samhobbs.key
And this command will set it so that only the root user can read and modify it:
sudo chmod 600 /etc/ssl/private/samhobbs.key
Most services like Apache, Postfix etc. require root privileges to start up. They read the certs when they start and store them in RAM, so that they can still use them when they drop to their normal users ( e.g. www-datafor Apache). Unlike your key file, your signed certificate file is not a secret (it is sent to users when establishing a secure session). You want all users to be able to read the cert, but only the root user to have write access to it. As before, this command will set it to be owned by root:
sudo chown root:root /etc/ssl/certs/samhobbs.crt
And this command will set it to be readable by everyone, but only modified by root:
sudo chmod 644 /etc/ssl/certs/samhobbs.crt
Some common SSL cert configuration parameters: Apache, Postfix, Dovecot
This section is a quick reference for where to find SSL parameters for Apache, Postfix and Dovecot.
Apache
You can tell Apache to use a specific certificate file in your SSL virtualhost configuration (e.g /etc/apache2/sites-available/default-ssl) with these parameters:
SSLEngine on SSLCertificateFile /etc/ssl/certs/samhobbs.crt SSLCertificateKeyFile /etc/ssl/private/samhobbs.key
Then reload Apache:
sudo service apache2 reload
Postfix
Postfix' SSL cert configuration can be found in /etc/postfix/main.cf:
smtpd_tls_cert_file=/etc/ssl/certs/samhobbs.crt smtpd_tls_key_file=/etc/ssl/private/samhobbs.key
...and reload Postfix:
sudo service postfix reload
Dovecot
Dovecot's SSL configuration is in /etc/dovecot/conf.d/10-ssl.conf:
ssl_cert = </etc/ssl/certs/samhobbs.crt ssl_key = </etc/ssl/private/samhobbs.key
NB: the < at the start of the path isn't an error, if you miss it out Dovecot won't load. Reload dovecot:
sudo service dovecot reload
Hopefully you found that useful! If you have anything to add or a question, please feel free to leave a comment!
Comments
In the Submitting the CSR to
In the Submitting the CSR to CAcert, the imported root certifcate is needed? I did all the work from Raspbian lite, so I cannot register from there. I have to register from another computer B, running Chromium OS . Do I need to have the imported root .crt in B?
CAcert signs its own root cert
I host my email for my domain
I host my email for my domain at google. I added root@mydomain as a second address at CACert account; they sent me a verify msg, with which I was able to verify my root@ address. But the crt generation page says it cannot verify I own the domain. So I asked it to probe root@mydomain at the site, which fails (because, I suspect, I host my emails at google). Is there a way to get my domain ownship verifed at CACert with google handling my emails?
Sorry, I don't know - I've
Hello Sam,
Hello Sam,
I created .crt for two .com domains. However when I try to generate the fingerprint on my rpi3 for those, the finger prints do not match the ones (for the corresponding domain) shown in the email. I used the following to generate the fingerprint
openssl x509 -noout -in all-neroth-com.crt -fingerprint -sha256
At the CAcert site, by clicking the advanced, I see that they use -sha256 as the default encryption.
Any suggestions?
PS. There is an important step needed before a certifcate can be generated. I needed to add the domain itself first at CAcert.
Domain -> add, specify domain name. They send a verify msg back. Click on the supplied link, then the domain gets added. Once a domain is added, and only after then, I could get the certificate. Perhaps CAcert added this new step after you had got yours.
Another note: I have .com and .org domains. I have only succeeded with the .com ones. .org domain add emails are not reaching me (yet).
Again, thank you for all your clear, precise tutorial!
Cordially, Chacko
After the CAcerts for my
After the CAcerts for my domains are put into the /etc/ssl/certs/ dir, is it not necessary to do c_rehash again?
Here is a link which says
Here is a link which says what I had mentioned in my last comment, that CAcert requires domain add first
http://www.lwithers.me.uk/articles/cacert.html
Hi Sam - your tutorials are
Hi Sam - your tutorials are the Best - Many thanks for all your hard work - much appreciated
Hi Sam,
Hi Sam,
Have seen a few other users have an issue with getting the their email verified. (root, postmaster etc). However, solutions provided did not help me :(
I am also struggling with this issue. Have checked my MX/A records, there are correct as far as I am concern. Have also checked the mail.log/mail.err files a million times and couldn't find any relevant record.
CAcert won't let me to add the root/postmaster email, and the error is:
****************
Email Address given was invalid, or a test connection couldn't be made to your server, or the server rejected the email address as invalid
Failed to make a connection to the mail server
****************
Can you please help?
Thanks, Saeed
Check log to see if connection attempt was made
sudo newaliasesbefore requesting the email? SamHi Sam,
Hi Sam,
Thanks for your reply.
Nothing hit the log file, strange!
Yes I did all the above. I have doubled check my MX/A records configuration, and everything was fine, except for one thing. You know that Ipv6 isn't static by their nature; I have found an extra records on my DNS records list as 'AAA' for Ipv6. I've removed it and problem has been solved. Successfully added the ssl certificate and it works fine. I thought it'd be worthwhile to share it with you and the others.
I reckon that CAcert was pinging my domain and didn't like the fact that 'AAA' record appeared to be configured.
Kind regards,
Saeed
ssl issue !
good morning Sam
I followed step by step the ssl creation document you have done , but i end up with my brother saying : www.chtracking.cf sent an invalid response.
ERR_SSL_PROTOCOL_ERROR
Here is a copy of the default-ssl.conf , i edit the lines :
SSLcertificateFile
SSLcertificateKeyFile
and
SSLcertificateChaineFile
can you tell me what i have done wrong ?
ServerAdmin webmaster@localhost
DocumentRoot /var/www/html
# Available loglevels: trace8, ..., trace1, debug, info, notice, warn,
# error, crit, alert, emerg.
# It is also possible to configure the loglevel for particular
# modules, e.g.
#LogLevel info ssl:warn
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
# For most configuration files from conf-available/, which are
# enabled or disabled at a global level, it is possible to
# include a line for only one particular virtual host. For example the
# following line enables the CGI configuration for this host only
# after it has been globally disabled with "a2disconf".
#Include conf-available/serve-cgi-bin.conf
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# A self-signed (snakeoil) certificate can be created by installing
# the ssl-cert package. See
# /usr/share/doc/apache2/README.Debian.gz for more info.
# If both key and certificate are stored in the same file, only the
# SSLCertificateFile directive is needed.
SSLCertificateFile /etc/ssl/certs/chtracking.crt
SSLCertificateKeyFile /etc/ssl/private/maclef2.key
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
SSLCertificateChainFile /etc//ssl/certs/chtracking.crt
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
# Note: Inside SSLCACertificatePath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCACertificatePath /etc/ssl/certs/
#SSLCACertificateFile /etc/apache2/ssl.crt/ca-bundle.crt
# Certificate Revocation Lists (CRL):
# Set the CA revocation path where to find CA CRLs for client
thank you !
( raspberry jessy)
Charles
issues with https
Sam,
I followed your tutorials and am now running my own email server on a Raspberry Pi. When I use Chrome from a computer outside my network to access Squirrelmail, it gives the certificate warning but then crosses out the https in the address bar when I advance against Chrome's recommendation. I am apprehensive to put in my username and password in Squirrelmail. Am I really still using SSL or could someone using Wireshark or the likes see my password in plain text?
Best,
Marta
Still encrypted but not guaranteed to be your site
About "Submitting the CSR to
About "Submitting the CSR to CAcert: First things first, you will need to go to the CAcert website and create an account".
There is a step which is not quoted in the guide, CA-Cert asks me to verify first the domain I submitted in the .csr file. To validate a domain it asks me to send a verification mail to one of the provided addresses:
- root@my-domain.com
- hostmaster@my-domain.com
- postmaster@my-domain.com
- admin@my-domain.com
- webmaster@my-domain.com
I tried to all the given emails but the provided error is always the same: "Email Address given was invalid, or a test connection couldn't be made to your server, or the server rejected the email address as invalid. Failed to make a connection to the mail server"
How to solve this?
Thanks
Regards
Nicola,
- Are your DNS records correct?
- Have you set up aliases as described in this tutorial, and run "sudo newaliases"?
- If you are still having issues, what do you see in the mail log (
Sam/var/log/mail.log) when cacert attempts to send you an email?Email Address given was invalid - CA Cert
Hi Sam
FOr some reason when trying to register with CaCert I get the following ...
Email Address given was invalid, or a test connection couldn't be made to your server, or the server rejected the email address as invalid
Failed to make a connection to the mail server
Email address is richard@stent.nz which is a functioning Raspberry Pi postfix / dovecot SMTP email running on port 465 of server caruxapp04.carluke.stent.nz
Please advise as I assume I need to register using this stent.nz domain.
Cheers Richard.
What do you see in the logs
what I see in /etc/log/mail.log when cacert tries to connect ...
Jun 12 12:10:15 caruxapp04 postfix/smtpd[1205]: connect from www.cacert.org[213.154.225.245]
Jun 12 12:10:17 caruxapp04 postfix/smtpd[1205]: lost connection after STARTTLS from www.cacert.org[213.154.225.245]
Jun 12 12:10:17 caruxapp04 postfix/smtpd[1205]: disconnect from www.cacert.org[213.154.225.245]
Appreciate your help with this Sam. Richard.
updated master.cf but still no luck
I have also tried again following an update to master.cf (commented out restrictions) and then reloading postfix
smtps inet n - - - - smtpd
-o syslog_name=postfix/smtps
-o smtpd_tls_wrappermode=yes
# -o smtpd_recipient_restrictions=permit_sasl_authenticated,reject
... but cacert request still 'lost connection after STARTTLviewS ...'
Richard.
what I now see in the verbose mail log
Hi Sam
I added CaCert source ip address to the debug_peer_list in main.cf to get more information about what my email domain is being rejected.
Below is /var/log/mail.log for another attempt. still has not provided me with any further clues why is was rejecting.
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: connect from www.cacert.org[213.154.225.245]
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: match_hostname: www.cacert.org ~? 127.0.0.0/8
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: match_hostname: www.cacert.org ~? [::ffff:127.0.0.0]/104
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: match_hostname: www.cacert.org ~? [::1]/128
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: match_list_match: www.cacert.org: no match
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 220 caruxapp04.carluke.stent.nz ESMTP Postfix (Raspbian)
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: < www.cacert.org[213.154.225.245]: EHLO www.cacert.org
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: match_list_match: www.cacert.org: no match
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-caruxapp04.carluke.stent.nz
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-PIPELINING
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-SIZE 10240000
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-VRFY
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-ETRN
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-STARTTLS
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-ENHANCEDSTATUSCODES
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250-8BITMIME
Jun 15 11:54:32 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 250 DSN
Jun 15 11:54:33 caruxapp04 postfix/smtpd[13880]: < www.cacert.org[213.154.225.245]: STARTTLS
Jun 15 11:54:33 caruxapp04 postfix/smtpd[13880]: > www.cacert.org[213.154.225.245]: 220 2.0.0 Ready to start TLS
Jun 15 11:54:34 caruxapp04 postfix/smtpd[13880]: match_hostname: www.cacert.org ~? 127.0.0.0/8
Jun 15 11:54:34 caruxapp04 postfix/smtpd[13880]: match_hostname: www.cacert.org ~? [::ffff:127.0.0.0]/104
Jun 15 11:54:34 caruxapp04 postfix/smtpd[13880]: match_hostname: www.cacert.org ~? [::1]/128
Jun 15 11:54:34 caruxapp04 postfix/smtpd[13880]: match_list_match: www.cacert.org: no match
Jun 15 11:54:34 caruxapp04 postfix/smtpd[13880]: lost connection after STARTTLS from www.cacert.org[213.154.225.245]
Jun 15 11:54:34 caruxapp04 postfix/smtpd[13880]: disconnect from www.cacert.org[213.154.225.245]
Looking forward to hearing if you have any solution or further suggestions for resolution.
Richard.
Maybe it's checking the common name on the cert
the cert are I using at the moment
In Postfix I am still using the snakeoil cert as I have not been able to generate my own trusted cert (crt or pem) as I need to have registered my stent.nz domain with CACERT in order to login and paste my CSR. I did register with another email address (my work email) and passphrase and then when I pasted my CSR is still that *.stent.nz was not a registered domain so it rejected. So I am a bit stuck!
In dovecot I am using the generated dovecot.pem (as per the tutorial) so that should work as I assume cacert is connecting via port 93.
How do I generate a val
From CACERT ...
The following hostnames were rejected because the system couldn't link them to your account, if they are valid please verify the domains against your account.
Rejected: *.stent.nz
generated by own self signed cert ... AND ...
OK, so it looks like your tutorial missed how I should explicitly create a self signed cert (stentnz.crt). I did this with "openssl x509 -req -days 365 -in stentnz.csr -signkey stentnz.key -out stentnz.crt" and then installed the reference to the cert in main.cf and then tried the CACERT registration again and still no luck ... but much more is logged but still no clue to me what the issue is ...
/var/log/mail.log (verbose) contains the following ...
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: connect from www.cacert.org[213.154.225.245]
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: smtp_stream_setup: maxtime=300 enable_deadline=0
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_hostname: www.cacert.org ~? 127.0.0.0/8
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_hostaddr: 213.154.225.245 ~? 127.0.0.0/8
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_hostname: www.cacert.org ~? [::ffff:127.0.0.0]/104
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_hostaddr: 213.154.225.245 ~? [::ffff:127.0.0.0]/104
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_hostname: www.cacert.org ~? [::1]/128
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_hostaddr: 213.154.225.245 ~? [::1]/128
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_list_match: www.cacert.org: no match
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_list_match: 213.154.225.245: no match
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: auto_clnt_open: connected to private/anvil
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: send attr request = connect
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: send attr ident = smtp:213.154.225.245
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/anvil: wanted attribute: status
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: status
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute value: 0
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/anvil: wanted attribute: count
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: count
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute value: 1
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/anvil: wanted attribute: rate
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: rate
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute value: 1
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/anvil: wanted attribute: (list terminator)
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: (end)
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 220 caruxapp04.carluke.stent.nz ESMTP Postfix (Raspbian)
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: watchdog_pat: 0x55cd4d90
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: < www.cacert.org[213.154.225.245]: EHLO www.cacert.org
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_list_match: www.cacert.org: no match
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: match_list_match: 213.154.225.245: no match
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-caruxapp04.carluke.stent.nz
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-PIPELINING
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-SIZE 10240000
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-VRFY
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-ETRN
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-STARTTLS
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-ENHANCEDSTATUSCODES
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250-8BITMIME
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 250 DSN
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: watchdog_pat: 0x55cd4d90
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: < www.cacert.org[213.154.225.245]: STARTTLS
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: > www.cacert.org[213.154.225.245]: 220 2.0.0 Ready to start TLS
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: send attr request = seed
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: send attr size = 32
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/tlsmgr: wanted attribute: status
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: status
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute value: 0
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/tlsmgr: wanted attribute: seed
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: seed
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute value: XAPQD5R+IYEWcAKpmd9jGWDPAp2/HGMPVfGDllS8g7M=
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: private/tlsmgr: wanted attribute: (list terminator)
Jun 20 15:55:44 caruxapp04 postfix/smtpd[9645]: input attribute name: (end)
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: send attr request = tktkey
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: send attr keyname = [data 0 bytes]
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: private/tlsmgr: wanted attribute: status
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute name: status
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute value: 0
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: private/tlsmgr: wanted attribute: keybuf
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute name: keybuf
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute value: XowhEvA2jxmYk+7L3YKoogaQpNrC9NFVQK5fLGachABukEG0tG9B9KGA9QKUzde5SNcpWw==
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: private/tlsmgr: wanted attribute: (list terminator)
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute name: (end)
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_create: SASL service=smtp, realm=(null)
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: name_mask: noanonymous
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: Connecting
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: VERSION?1?1
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: MECH?PLAIN?plaintext
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: name_mask: plaintext
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: MECH?LOGIN?plaintext
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: name_mask: plaintext
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: SPID?11223
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: CUID?7
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: COOKIE?264700a991f3cfbe99b534be5ea07fdd
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_connect: auth reply: DONE
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_mech_filter: keep mechanism: PLAIN
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: xsasl_dovecot_server_mech_filter: keep mechanism: LOGIN
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: watchdog_pat: 0x55cd4d90
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: smtp_get: EOF
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_hostname: www.cacert.org ~? 127.0.0.0/8
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_hostaddr: 213.154.225.245 ~? 127.0.0.0/8
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_hostname: www.cacert.org ~? [::ffff:127.0.0.0]/104
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_hostaddr: 213.154.225.245 ~? [::ffff:127.0.0.0]/104
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_hostname: www.cacert.org ~? [::1]/128
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_hostaddr: 213.154.225.245 ~? [::1]/128
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_list_match: www.cacert.org: no match
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: match_list_match: 213.154.225.245: no match
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: send attr request = disconnect
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: send attr ident = smtp:213.154.225.245
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: private/anvil: wanted attribute: status
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute name: status
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute value: 0
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: private/anvil: wanted attribute: (list terminator)
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: input attribute name: (end)
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: lost connection after STARTTLS from www.cacert.org[213.154.225.245]
Jun 20 15:55:45 caruxapp04 postfix/smtpd[9645]: disconnect from www.cacert.org[213.154.225.245]
CAcerts
I have installed dovecot and postfix (not squirrelmail, yet) and have two mail addresses "mike@whenpigsfly.hopto.org" and "webmaster@whenpigsfly.hopto.org" I'm using NOIP. Anyway, I can send and receive email on both using K9 and Thunderbird. For some strange reason CAcert cannot communicate with either email address. What can I do now to complete an account set-up for CAcert?
What do you see in the logs?
having trouble setting up a acount on CAcert
Hi Sam,
I have followed your manual. For the second time even and I want to complement you! Its the best, even learning something. Its fun to do.
But now I want to make a signed cert at CAcert and I'am trying to get a account, but a the form appying for one. I enter my email adress as you said postmaster, webmaster or root. Did all the aliases. And CAcert keeps saying
The e-mail address you entered is invalid, or a test connection could not be established with your server, or the server has the e-mail address as invalid.
Could not connect to the mail server
This is weird becouse I can connect to my mailserver. No problem. And all the alliases exist. Even a user called webmaster.
Do you have any idea?
On the flipside can you also use letsencrypt? Or are there any downsides?
Thanks in advance.
DNS records
yes
Yes I can send email from gmail. I receive email from... well everybody.
What's in the logs from CAcert
Add new comment