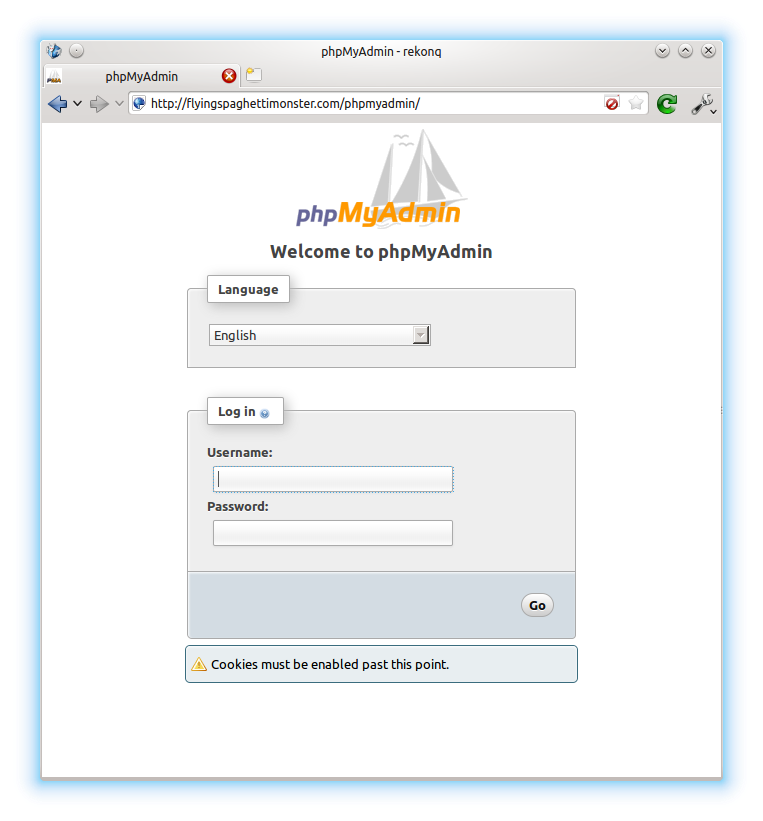
 I recently installed a plugin for WordPress called “Better WP Security”. One of the features this plugin has is the ability to log all 404 errors, and temporarily or permanently block hosts that request too many non-existent pages in a short space of time. This is useful for blocking scripts that try to guess the location of your admin pages and then brute force their way in or exploit some specific vulnerability in the software. I noticed in the logs that one particular script (“w00tw00t.at.blackhats.romanian.anti-sec:)”) was checking my website to see if phpmyadmin had been installed but the setup script not run, requesting lots of pages like “phpMyAdmin/scripts/setup.php”. This got me thinking about securing the phpMyAdmin page a little, as I had pretty much just set it up and forgotten about it. I very rarely use it, but still wanted it installed just in case. So, the best solution was to simply disable access from outside my LAN.
I recently installed a plugin for WordPress called “Better WP Security”. One of the features this plugin has is the ability to log all 404 errors, and temporarily or permanently block hosts that request too many non-existent pages in a short space of time. This is useful for blocking scripts that try to guess the location of your admin pages and then brute force their way in or exploit some specific vulnerability in the software. I noticed in the logs that one particular script (“w00tw00t.at.blackhats.romanian.anti-sec:)”) was checking my website to see if phpmyadmin had been installed but the setup script not run, requesting lots of pages like “phpMyAdmin/scripts/setup.php”. This got me thinking about securing the phpMyAdmin page a little, as I had pretty much just set it up and forgotten about it. I very rarely use it, but still wanted it installed just in case. So, the best solution was to simply disable access from outside my LAN.
Here’s how:
phpMyAdmin has its own Apache configuration file that Apache loads when it starts, which is found here: /etc/phpmyadmin/apache.conf. Inside this file you can define access rules to phpMyAdmin based on IP address ranges. Open it in a text editor (sudo nano /etc/phpmyadmin/apache.conf) and find the block that looks like:
<Directory /usr/share/phpmyadmin> ... </Directory>
Inside the block, add the following lines:
Order Deny,Allow Deny from all Allow from 127.0.0.1 Allow from 192.168.1.0/24
i.e. deny the request to send the login page unless it comes from:
- your server, or
- anyone with an IP address 192.168.1.* (0/24 is like a wildcard), i.e. someone on your LAN.
If your router’s IP address is not 192.168.1.1, but 192.168.0.1, then change the third line to “Allow from 192.168.0.0/24“. Reload apache (sudo service apache2 reload) and you’re done. You can test the rules out by going to your phpMyAdmin page in your mobile’s browser, or a device that isn’t connected to your router.
Comments
Restrict Access to phpMyAdmin from WAN
Editing the /etc/phpmyadmin/apache.conf file to add the block:
Order Deny,Allow
Deny from all
Allow from 127.0.0.1
Allow from 192.168.1.0/24
produces and error upon reloading Apache:
$ sudo service apache2 reload
[FAIL] Reloading web server config: apache2 failed!
The offending line is the last line in the block:
Allow from 192.168.1.0/24
(my ip addresses different, of course)
Any idea on why? I would like to make my install as secure as possible.
F. Mitchell
Opelika, AL USA
The IP has to match your
The IP has to match your gateway/router IP
Hi Sam,
Thanks for the quick response.
My gateway is 10.0.1.1, I entered 10.0.1.1/100 thinking I was only allowing addresses from 10.0.1.1 up to 10.0.1.100 to connect. If I comment out this line apache starts no problem. This line in, and it fails to start with the error message in my original comment.
I have some static ip addresses assigned to higher addresses for my printers, scanners, etc.
I have followed your tutorials and have owncloud, a mail server, squirrelmail, and wordpress running on a Raspberry Pi 2. The server will only get very light use, a few emails and very little regular web access. I found your tutorials to be most helpful!
Thanks,
F. Mitchell
Opelika, AL US
Try 10.0.1.0/24
0/24as "*". Try 10.0.1.0/24 SamTry 10.0.1.0/24
Sorry Sam, the 1 was a typo, what i tried was 10.0.1.0/24.
Now that I know that the 24 does not refer to specific addresses, I will research it further also.
Thanks for you prompt response!!!
F. Mitchell
Opelika, AL USA
Try 10.0.1.0/24
Sam,
"The “0/24″ denotes wildcat (equivalent to * in Windows)" is what I was able to find. The explanation is from https://abuhawa.wordpress.com/2009/01/07/restrict-phpmyadmin-access-to-…
I went back and rechecked my editing, and I did have the typo '10.0.1.1/24'. Changed to 10.0.1.0/24 and the error went away!
Thanks!
Felton Mitchell
Opelika, AL USA
Great tutorial!
Thanks a bunch for this. I noticed in my Apache logs I had a ton of brute force attempts to login to my phpmyadmin page.
This worked great!
No problem, thanks for the
Add new comment